In today’s fast-paced digital world, managing information is a constant balancing act. Data flows, access permissions shift, and the very nature of how and when information is available can change in an instant. Whether it’s due to new regulations, system upgrades, personnel changes, or simply a reevaluation of data sensitivity, ensuring that everyone knows the current status of information availability is crucial for operational efficiency and security.
Without a clear, standardized way to document these shifts, organizations can quickly find themselves in a tangle of confusion, potential compliance breaches, and frustrated employees. This is where a dedicated form comes into play, providing a structured mechanism to communicate and approve necessary adjustments.
Understanding the Need for Information Availability Adjustments
Think about how many pieces of information your organization handles daily. From customer records to internal strategic plans, each piece has an associated level of availability. This could mean who can see it, when they can see it, and under what circumstances. But these aren’t static definitions. Business needs evolve, legal landscapes shift, and technology advances, all of which can necessitate a change in how information is accessed and used.
Imagine a scenario where a new data privacy regulation comes into effect, requiring a tighter restriction on certain personal information. Or perhaps a project concludes, and sensitive documents that were widely accessible during development now need to be archived and access limited. Without a formal process, these changes might be communicated verbally, via informal emails, or simply forgotten, leading to risks.
The absence of a standardized procedure for altering information availability can lead to serious headaches. You might encounter data breaches due to over-accessibility, compliance failures, or even operational bottlenecks because authorized personnel can’t find the information they need due to unannounced restrictions. A robust form ensures that every modification is documented, approved, and communicated effectively.
It’s like having a master switchboard for all your data, where every alteration to its on or off status is logged and accounted for. This not only mitigates risks but also builds a culture of accountability and transparency around information governance, ensuring that your organization remains agile and secure.
Common Scenarios Requiring Updates
- Legal and Regulatory Compliance: New laws (like GDPR or CCPA) often dictate stricter data handling, requiring immediate adjustments to information availability.
- Security Enhancements: Following a security audit, certain data sets might need reduced access to bolster overall protection against threats.
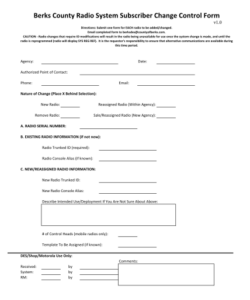
- Operational Changes: A department restructuring might mean some teams no longer need access to specific data, or new teams require it.
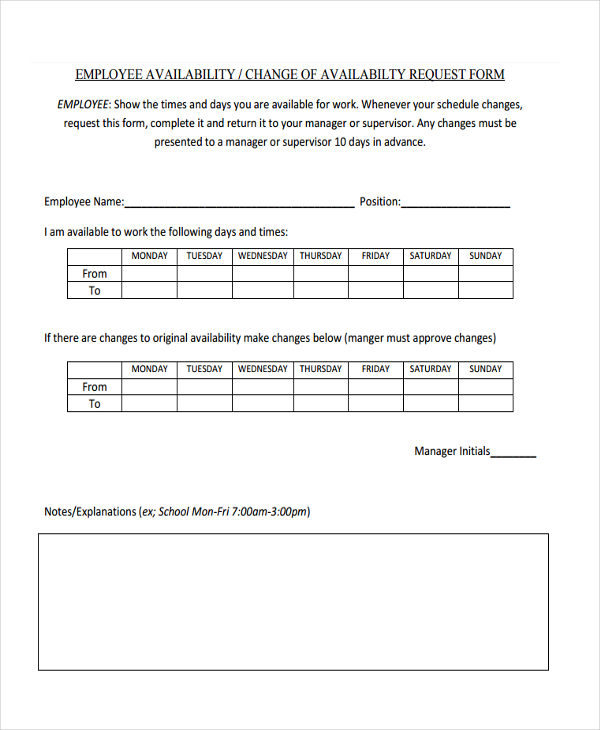
- Personnel Updates: When employees join, leave, or change roles, their information access permissions must be updated accordingly.
- Data Classification Revisions: Information that was once deemed low sensitivity might be reclassified as high, necessitating restricted availability.
Crafting Your Ideal Change of Information Availability Form Template
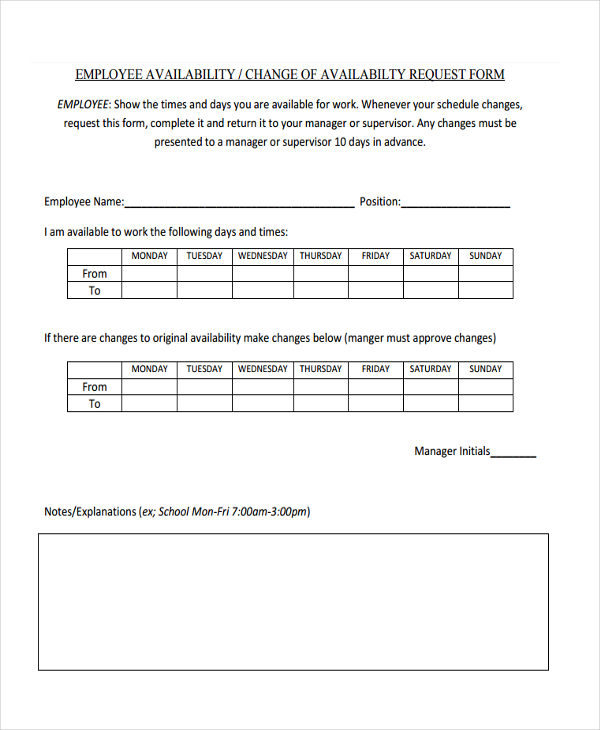
Now that we understand why a form like this is so critical, let’s explore what goes into making an effective one. A well-designed change of information availability form template isn’t just a piece of paper; it’s a critical tool for managing your organization’s most valuable assets. It should be intuitive, comprehensive, and facilitate a smooth workflow from request to approval and implementation.
The key is to include all necessary fields without making it overly cumbersome. It needs to capture the essence of the change, the justification, and the necessary approvals. Think about who will be filling it out and who will be reviewing it. Clarity and conciseness are paramount to ensure adoption and accuracy.
Your template should guide the user through the process, prompting them for all the relevant details. This includes identifying the specific information affected, detailing the current and proposed availability levels, and explaining the rationale behind the change. This structured approach minimizes errors and ensures that all stakeholders have the information they need to make informed decisions.
Furthermore, integrating this form into your existing information governance or IT service management processes is crucial. It shouldn’t be a standalone document that gets lost; instead, it should be a fundamental part of your change management framework, ensuring that every modification to information availability is systematically handled.
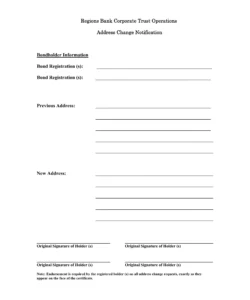
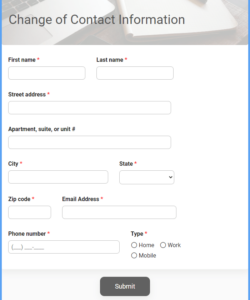
- Requester Information: Name, department, contact details.
- Date of Request: When the change was formally requested.
- Nature of Information: A clear description of the data set or information type affected.
- Current Availability Status: Detail who currently has access and how.
- Proposed Availability Change: Specify the desired new access levels (e.g., restrict to specific roles, broaden for a new project, temporary suspension).
- Reason for Change: A concise explanation of why this change is necessary (e.g., compliance, project completion, security enhancement).
- Effective Date of Change: When the new availability status should take effect.
- Approval Signatures: Designated sections for departmental heads, security officers, or IT managers to approve the change, including dates.
- Implementation Details: A section for IT or information managers to note how the change was implemented and by whom.
Implementing a standardized change of information availability form template helps in maintaining an up-to-date record of your data landscape. It provides a clear audit trail, which is invaluable for compliance, security reviews, and internal accountability. This systematic approach ensures that information access aligns perfectly with current organizational needs and regulatory requirements.
By streamlining the process for adjusting information availability, your organization can foster a more secure and efficient environment. It empowers employees to request necessary changes while ensuring that all modifications are properly vetted and documented. This reduces risk, improves operational flow, and builds greater confidence in your data management practices.